The Smart Contract Weakness Classification and Test Cases (SWC) Registry is a set of Web3 vulnerabilities to avoid when writing smart contracts. It may seem daunting to understand every issue so I’ll do my best to demystify every issue and explain each vulnerability with real-world examples. This write-up is intended for those who are just starting out in solidity development and smart contract auditing.
SWC-111: Use of Deprecated Solidity Functions
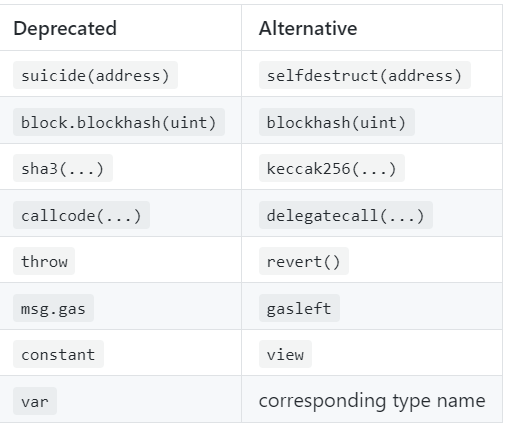
This vulnerability is pretty simple to understand. In short, some functions and keywords in Solidity are deprecated (not in use anymore) as Solidity continues to upgrade its versions. With new major versions of the Solidity compiler, deprecated functions and operators may result in side effects and compile errors. Don’t worry about the workaround of all the deprecated keywords and functions as Solidity provides alternatives to the deprecated constructions.
Here is the list of the deprecated keywords and functions and their alternatives.
It is always good to keep up with the latest changes in Solidity.
References:
https://docs.soliditylang.org/en/v0.8.19/050-breaking-changes.html
https://swcregistry.io/docs/SWC-111
Thank you for reading! If you have any questions or clarifications, do reach out to @cryptostaker22 on Twitter or cryptostaker#1621 on Discord. Have a great week ahead!